April 18, 2022
Beosin’s Analysis of the Beanstalk Exploit
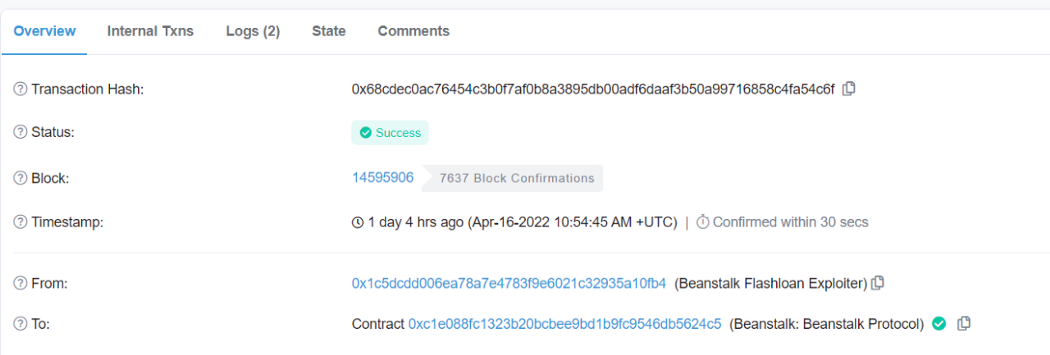
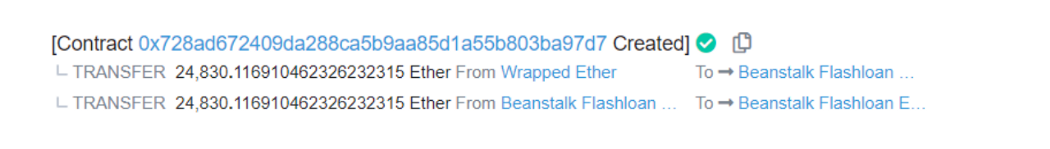
On April 17th, 2022, according to Beosin EagleEye, Beanstalk’s Beanstalk Protocol contract was exploited for about 24,830 ETH. Beosin security team analyzed the incident and the findings are shown below.
Beanstalk Introduction
Beanstalk is a decentralized stablecoin-based protocol. The official website: https://bean.money.
Relevant Information
Transaction hash:
0xcd314668aaa9bbfebaf1a0bd2b6553d01dd58899c508d4729fa7311dc5d33ad7
Exploiter’s address:
0x1c5dcdd006ea78a7e4783f9e6021c32935a10fb4
Contract that launched the hack:
0x79224bC0bf70EC34F0ef56ed8251619499a59dEf
Victim contract:
0xc1e088fc1323b20bcbee9bd1b9fc9546db5624c5
Exploitation Flow
1.The hacker initiated a proposal one day before the attack, and the proposal will withdraw funds from Beanstalk: Beanstalk Protocol contract once passed.
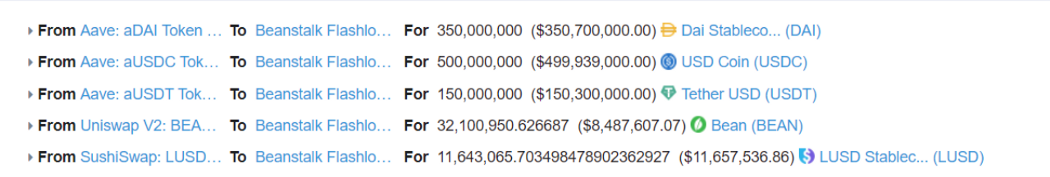
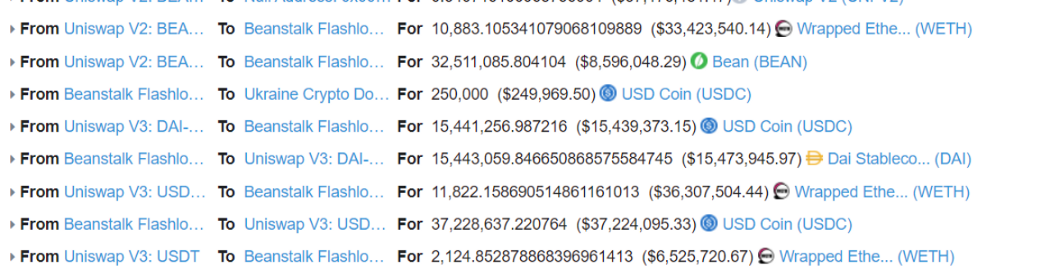
2. The hacker exchanged 350,000,000 DAI, 500,000,000 USDC, 150,000,000 USDT, 32,100,950 BEAN and 11,643,065 LUSD as a reserve of funds through flashloan.
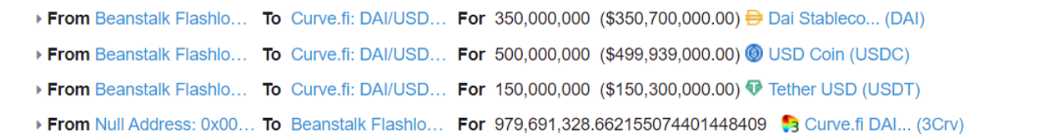
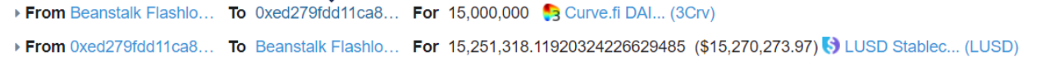
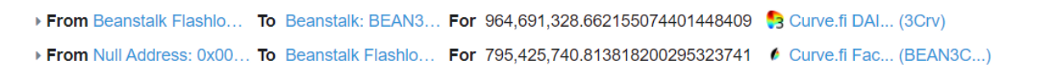
3. Added DAI, USDC, USDT funds from step-2 in Curve.fi DAI/USDC/USDT trading pool as 979,691,328 3Crv liquidity tokens, swapping 15,000,000 3Crv for 15,251,318 LUSD.
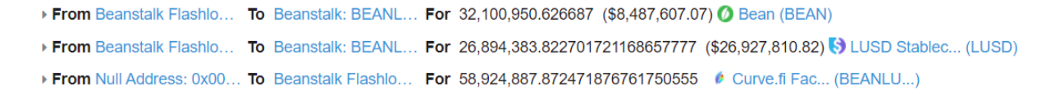
4. Converted 964,691,328 3Crv tokens into 795,425,740 BEAN3CRV-f for voting and added liquidity to 32,100,950 BEAN and 26,894,383 LUSD to get 58,924,887 BEANLUSD-f liquidity tokens.
5. The hacker used BEAN3CRV-f and BEANLUSD-f from step 4 to vote on the proposal, resulting in the proposal passing. Thus the Beanstalk: Beanstalk Protocol contract transferred 36,084,584 BEANs, 0.54 UNI-V2s, 874,663,982 BEAN3CRV-fs, and 60,562,844 BEANLUSD-fs to the contract deployed by the hacker.

6. Finally the hacker removed liquidity and returned the flashloan, converting the profited tokens into 24,830 ETH and transferred to the hacker’s address.
Vulnerability Analysis
This attack mainly exploits the fact that the votes in the voting contract are obtained based on the number of tokens held in the account.
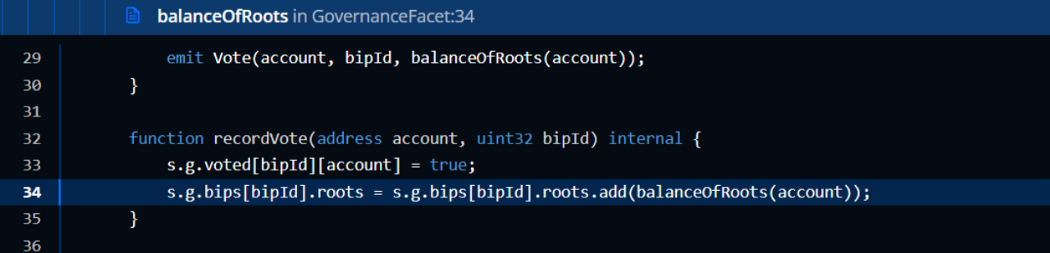
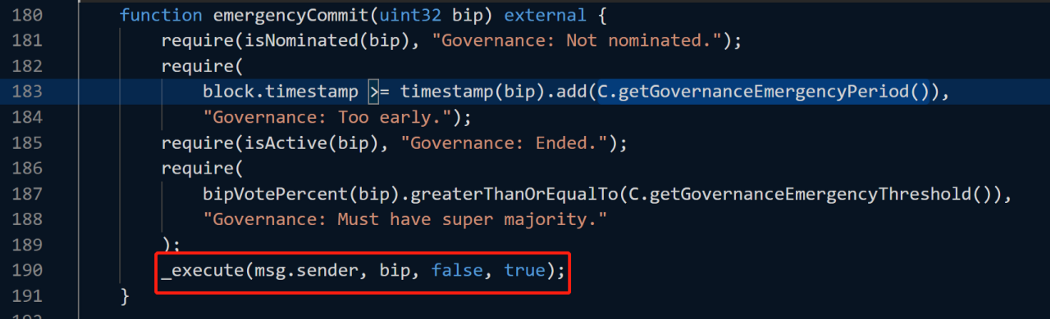
The attacker initiates the proposal to withdraw funds from Beanstalk: Beanstalk Protocol at least a day ago, and then calls emergencyCommit for an emergency commit to execute the proposal, which is the reason why the hacker started preparation 1 day before.
Fund Tracing
As of this writing, the hacker have profited 220,296,601 USDC, 14,742,429 DAI, 6,603,829 USDT, 0.5407 UNI-V2, and $640,224 in BAEN tokens, for a total of nearly $80 million. The 250,000 USDC was donated to Ukraine Crypto Donation during the attack, then the stolen funds were converted to ETH and continued to be deposited to Tornado.Cash.
Summary
In response to this incident, Beosin security team recommends:
1. The funds used for voting should be locked in the contract for a certain period of time and avoid using the current fund balance to count the number of votes in order to avoid possible repeated voting and the use of flashloans for voting.
2. Project parties and the community should pay attention to all proposals, and if the proposal is a malicious proposal, it is recommended that timely measures should be taken during the proposal voting period to deprecate the proposal and prohibit it from receiving votes as well as being executed.
3. Banning contract addresses from voting can be taken into account.
4. Before the project goes live, it is highly recommended to choose a professional security audit company to conduct a comprehensive security audit to avoid security risks.
If you have need any blockchain security services, please contact us:
Related Project
Related Project Secure Score
Guess you like
2omb 3omb is currently being targeted by an arbitrage flash loan attack.
April 18, 2022

Beosin VaaS — Smart Contract Automatic Detection Tool Officially Launched!
April 14, 2022

Beosin Blockchain Security Ecosystem Overview in Q1 2022
April 14, 2022
Beosin: Analysis of the Attack on Gymdefi
April 10, 2022
