April 24, 2022
How to Ensure the Security of NFT Under the Web 3.0 Boom?
Nowadays, the explosive growth of NFT is boosting the development of Web 3.0. In the past, Web 1.0 to Web 2.0 has realized the transformation of content from consumers to producers, and its essence is a great migration from the physical world to the network world in parallel time and space. Then in the Web 3.0 world, each user is in control of his or her own data, identity and destiny, and a new generation of Internet is created.
Web 3.0 exists on the basis of blockchain, promising to return privacy and digital identity to users, while enabling new levels of interaction thanks to applications such as NFTs. But what we need to pay more attention to is the hidden security issues of NFT under the Web 3.0 boom, as evidenced by the recent “hacking incidents” that have been seen everywhere in the NFT space.
Ⅰ What NFT contract exploits have recently occurred?
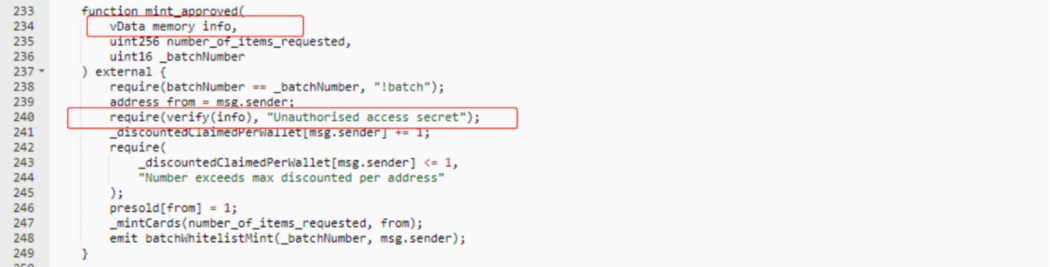
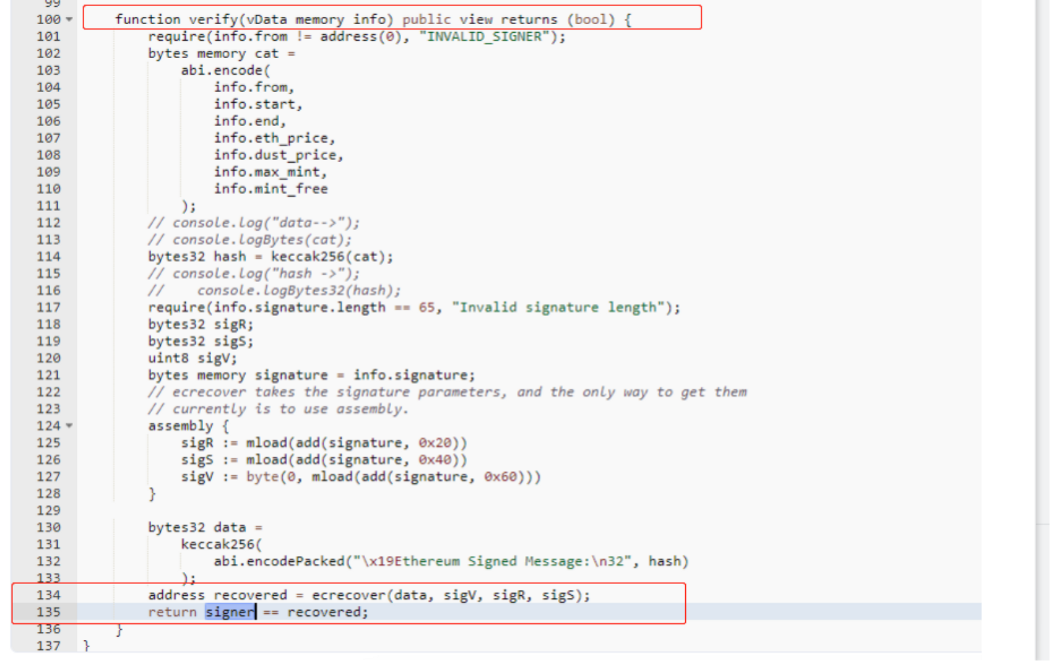
On April 20, The Association NFTs (NBA) were exploited due to a contract vulnerability. In the contract code, the vData memory parameter info is not verified in the function that passed in, resulting in a reusable signature, and users can use someone else’s signature to mint NFTs.
On April 23, 2022, the NTF project Akutar’s AkuAuction contract has locked 11,539 ETH (worth ~$34 million) permanently due to vulnerabilities in the smart contract itself. After analysis by Beosin security team, we found two vulnerabilities in Akutar’s contract.
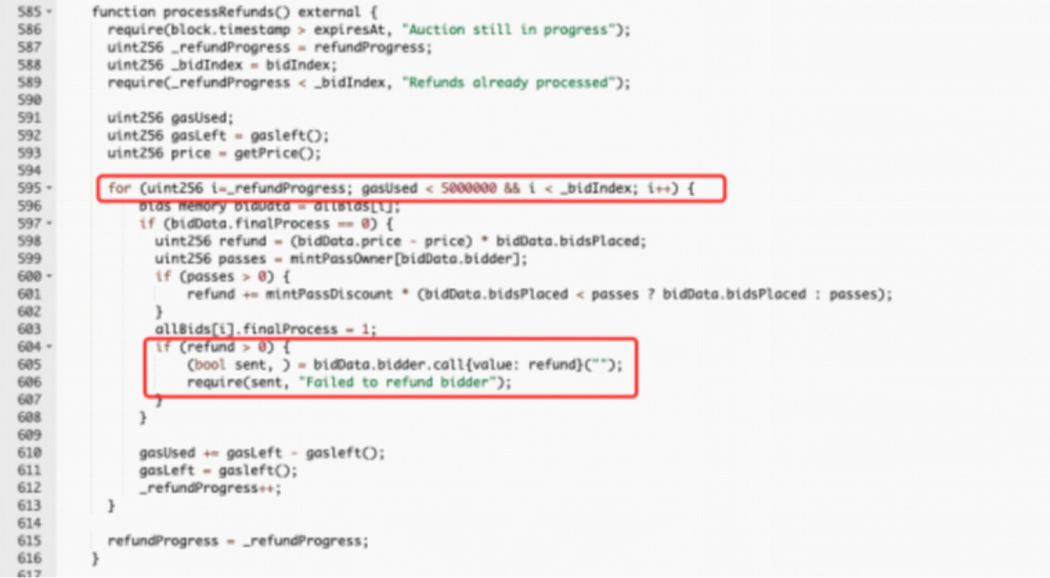
The first vulnerability is in processRefunds, where the designer performs a loop-refund based on refundProgress. However, if there is an attacker at this time in the fallback to revert, it will lead to the subsequent people cannot be refunded. This vulnerability was proved on chain but not exploited.
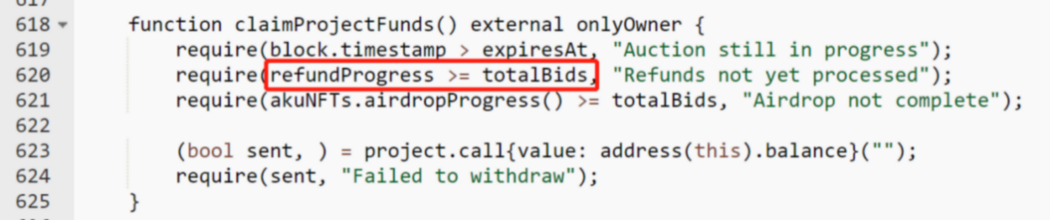
The second vulnerability is in claimProjectFunds, where the totalBids variable of the require statement (refundProgress > = totalBids) should be bidIndex, and this vulnerability makes this judgment condition fail forever, resulting in the inability to perform subsequent withdrawal operations. Ultimately, this resulted in the 11,539 ETH (worth approximately $34 million) being locked from withdrawal.
Therefore, it is becoming increasingly urgent to focus on NFT contract risks.
Ⅱ What are the common NFT contract issues?
According to NFTSCAN data, there are now nearly 70,000 NFT contract addresses worldwide, and the numbers continue to grow.
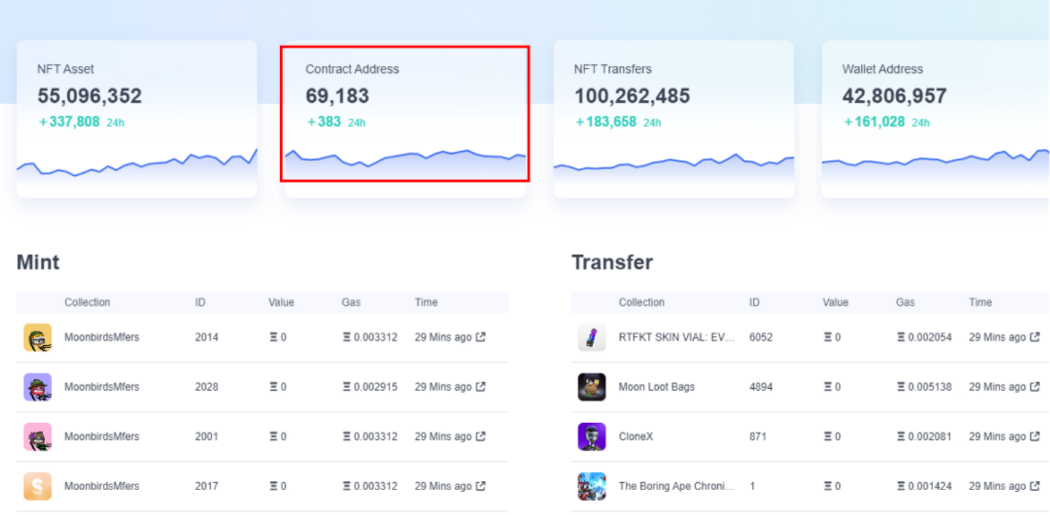
Data source: NFTSCAN (Updated: April 24 2022)
As the base of Web3.0, NFT’s security issues are equally important to the development of the blockchain industry. In order to escort the security ecosystem of Web3.0, Beosin VaaS has scanned thousands of NFT projects for vulnerabilities and found that the common contractual issues of NFT can be divided into the following categories.
Business logic related issues
Such issues can directly lead to errors in the business logic of the contract.
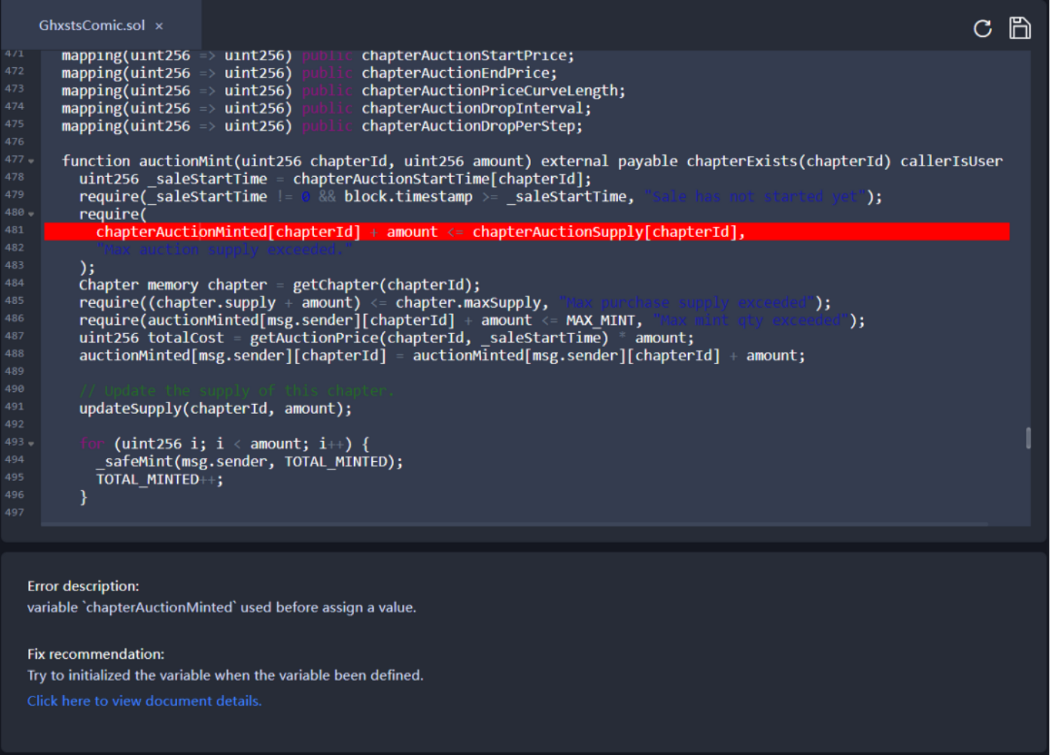
Vulnerability Description: The value of chapterAuctionMinted is always the initial value, but the value is used for conditional checking here. If Beosin VaaS is used for scanning during development phase, the developer can determine if the relevant logic is missing based on the results (which may lead to business logic issues such as NFT over-mintable), or redundant code.
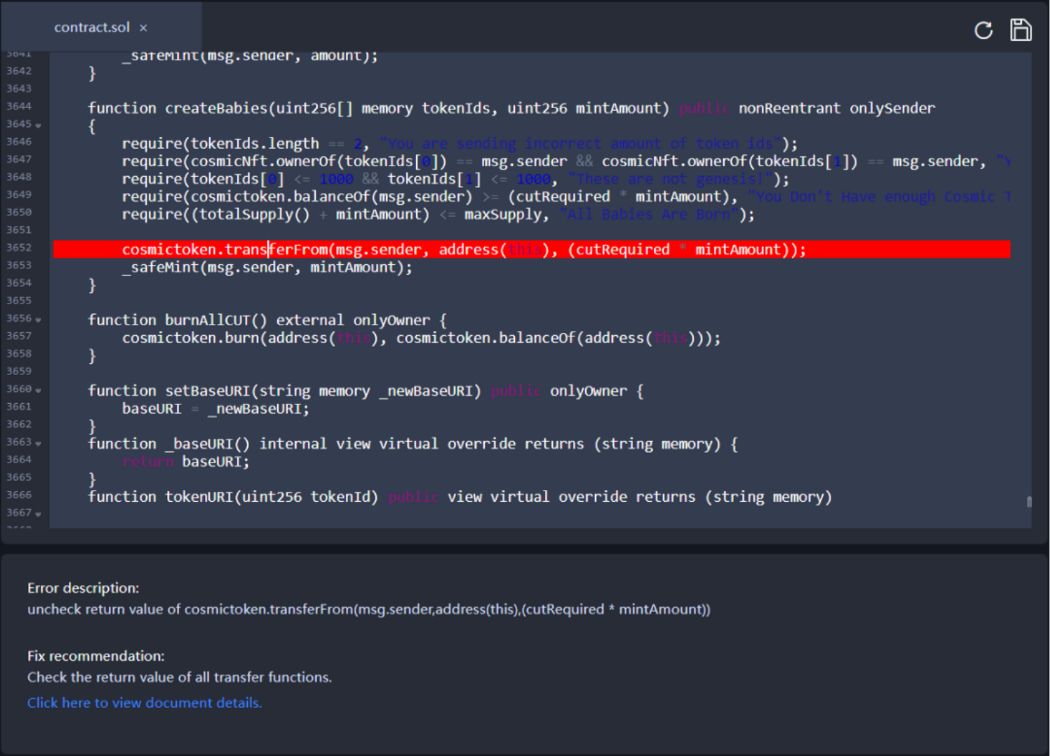
Vulnerability Description: Unchecked return value. Paid minting feature can often be seen in NFT projects, where the caller needs to send ERC20 tokens as a minting fee to the NFT minting contract, and then the NFT minting contract mint the corresponding number of NFT tokens for them. However, some ERC20 contracts have the problem of fake deposit, i.e., transfer failures do not throw an exception but return false, which leads to a problem that attackers can exploit it to mint any number of NFTs without paying the fee. Developers should check the return value of the transferFrom operation or use the safeTransferFrom function for ERC20 token transfers according to the recommendations by ‘Beosin VaaS’.
Coding standards related issues
Such issues may not directly cause errors in business logic, but they can affect the readability of the code, resulting in excess gas consumption in contract calls, etc. Also non-standard code tends to lead to logical confusion when writing, with a higher probability of having hidden logical errors.
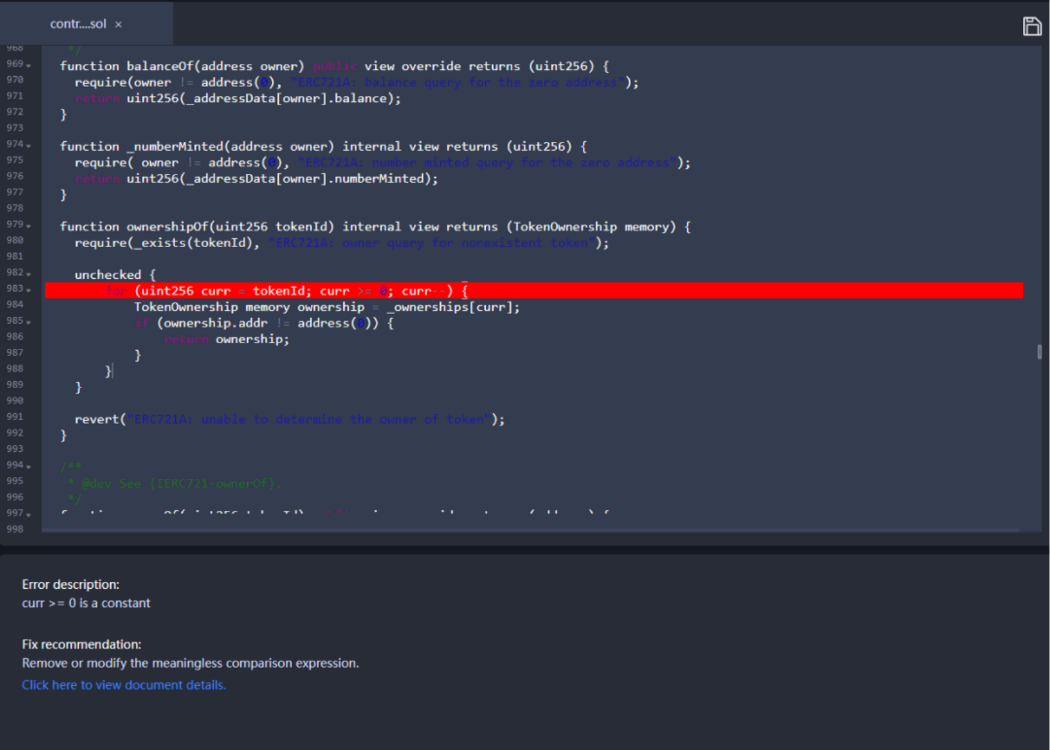
Vulnerability Description: The end condition of the loop here is curr>=0, and curr is uint which causes curr>=0 to be constantly satisfied. This will lead to the loop does not end properly. ‘Beosin VaaS’ will alert such fixed value of results, and users can confirm the logic here to delete or modify the condition.
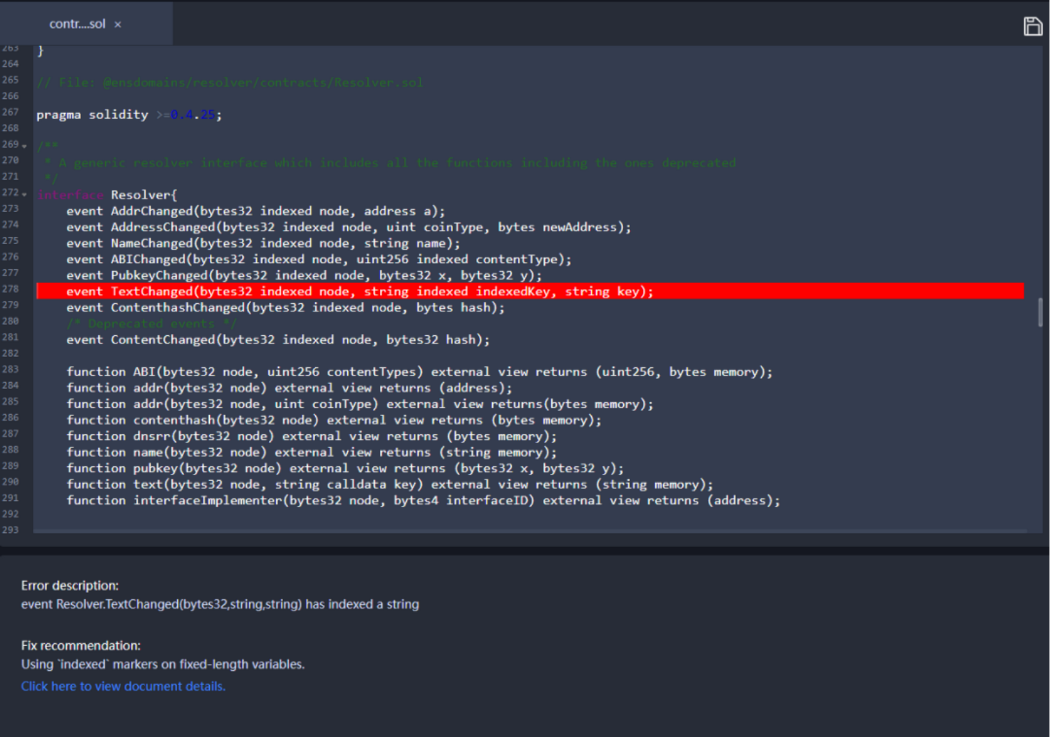
Vulnerability Description: Here the data of string type is marked with indexed in the event, and this will lead to not getting the corresponding string result directly in the event result. It is recommended that users refer to the recommenations in ‘Beosin VaaS’ and only use indexed to modify variables of fixed length.
Our research found that most of the NFT contracts have not been professionally audited, which poses a great security risk and can easily lead to attacks and loss of assets. NFT smart contract developers should pay attention to the correctness of codes when designing and implementing the contract. We highly recommend that after development is completed, devs can use ‘Beosin VaaS’ for security testing of the project. Before the project goes live, contract owners can choose a professional security audit to avoid security risks.
Security is an important guarantee for blockchain technology, and it is becoming more and more important to guard the security of Web 3.0. The business logic-related issues and code standards-related issues we talked about today are also common types of issues inside smart contracts, and we will continue to post NFT-related security reports. Stay tuned!
Before the project goes live, it is highly recommended to choose a professional security audit company to conduct a comprehensive security audit to avoid security risks.
If you have need any blockchain security services, please contact us:
Website Email Official Twitter Alert Telegram LinkedIn
Join Coinmonks Telegram Channel and Youtube Channel learn about crypto trading and investing
Also, Read
Related Project
Related Project Secure Score
Guess you like
Beosin Has Completed Security Audit Service of TribeOne
April 25, 2022
$34M Locked Due to Contract Vulnerabilities in Akutar: Beosin’s Full Analysis
April 23, 2022
Beosin’s Analysis of the ZEED Exploit
April 21, 2022

How to quickly track assets laundered by Hacker’s Paradise-Tornado Cash? Beosin may help you
April 21, 2022
